Internet Research Project
Privacy Risks in Data Collection and Storage
As usage of the internet grows more and more over the years, more and more people store and share their information online. However, it is important to understand the risks in privacy that can come with this dispense of data. Information online can be used for many things, both good and bad, and can sometimes be used without the consumer’s permission or knowledge.
Consumers may not have the full knowledge of where and who their information goes to when they share it online. For example, when companies are given sensitive information, such as names, social security numbers, credit card information, and mailing addresses, they can save it in their files without consumers knowing. They do this because these types of information are often needed to complete business functions.
A prime example of this happening is the Facebook-Cambridge Analytica Scandal that occurred in 2018. This came after it was revealed that data from millions of Facebook users were being accessed and shared with Cambridge Analytica. This, of course, angered millions and was very costly for Facebook.


Misuse and Protection of Computing Resources
The misuse of computing resources can be defined as the improper use of technology for non-intended purposes. The term can also be referred to as IT abuse, or informational technology abuse. Common examples of IT abuse can include the use of obscene language online, misuse of important property including electronic data and email, and the defacing/damaging of important records.
These methods of misusing computing resources can cause a lot of harm to many people. This harm can come in the form of loss of money from fraud, reputation damage from fake news/cyberbullying and legal punishments from cybercrime. However, there are ways to protect computing resources to make sure they are used right.
To protect the use of computing resources, companies use several strategies. These can include having antivirus software, frequent updates, and firewalls to protect against viruses. Backups are also a common way to preserve important information. Overall, the protection of computing resources is very important to stop the misuse of the same computing resources.


Unauthorized Access to Information
Hackers and malicious actors can gain unauthorized access to your information in many ways. One of the most common ways is phishing attacks. This is where the hacker uses fake information, such as emails, companies, or identities, to try and convince the consumer to reveal sensitive information.
Another common method hackers use to obtain your information is through malware. This can be done by installing unwanted software on your computer without you knowing. The hacker can then exploit the weaknesses on your computer to find you sensitive information and take it. It is important to have a firewall or antivirus to help protect your computer from this.
There are many other methods that can help you defeat hackers and protect from cyber attacks. First, you can use multi-factor authentication, or MFA for short. This requires there to be multiple checks before information can be accessed, increasing security. Another method is having backups for your most important files, just in case they are stolen and lost forever.


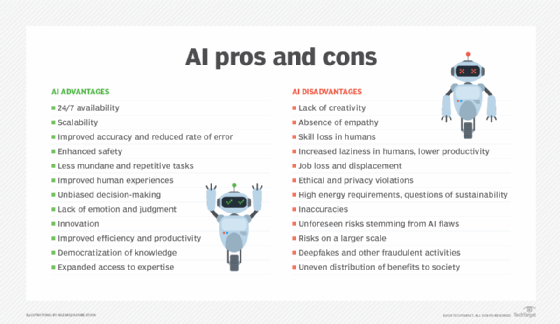
Benefits and Risks of Computing Innovations
Innovations in the technological world can come with many benefits, but they can also hold risks that hadn’t been thought of before. Risks in computing innovations come up often, and are due to the creator or innovator not being able to think of every possible way their innovation or product could be used.
One example of an unexpected risk of an innovation can be found in the phone. The phone was first created as a means of communication to have a small computer that you can carry around at all times. These are benefits that many people can’t live without today, but an unexpected risk that wasn’t thought of was the addiction that people would get.
Many people, especially the younger generation, are constantly on their phones and can be classified to have an addiction. This can affect their daily lives, whether that is school, work, or family. This addiction wasn’t thought of, or at least fully understood, before the phone was created, and now millions of people’s lives revolve around their phone.